Once malicious code runs, the attacker tries to reach the same places:
• File shares
• Credentials
• Databases
• Critical systems
Instead of trying to predict every attack technique, control what happens when unknown code executes.
If unknown files are automatically virtualized and isolated, the payload can run — but it cannot touch the real system.
🚫 No access to files
🚫 No access to credentials
🚫 No access to critical assets
The attack path stops there.
You don’t need to predict the attacker’s technique.
𝗬𝗼𝘂 𝗷𝘂𝘀𝘁 𝗻𝗲𝗲𝗱 𝘁𝗵𝗲 𝗯𝗹𝗮𝘀𝘁 𝗿𝗮𝗱𝗶𝘂𝘀 𝘁𝗼 𝗯𝗲 𝘇𝗲𝗿𝗼 𝘄𝗵𝗲𝗻 𝗰𝗼𝗱𝗲 𝗿𝘂𝗻𝘀.
𝗧𝗲𝗰𝗵𝗻𝗶𝗾𝘂𝗲𝘀 𝗰𝗵𝗮𝗻𝗴𝗲.
𝗧𝗵𝗲 𝗰𝗵𝗼𝗸𝗲 𝗽𝗼𝗶𝗻𝘁 𝗱𝗼𝗲𝘀𝗻’𝘁.
Source of Article:
Melih Abdulhayoglu
Founder & Executive Chairman @ Xcitium | Cyber Security, AI , ITSM
Melih Abdulhayoglu
Founder & Executive Chairman @ Xcitium | Cyber Security, AI , ITSM
Click here for more infor.




























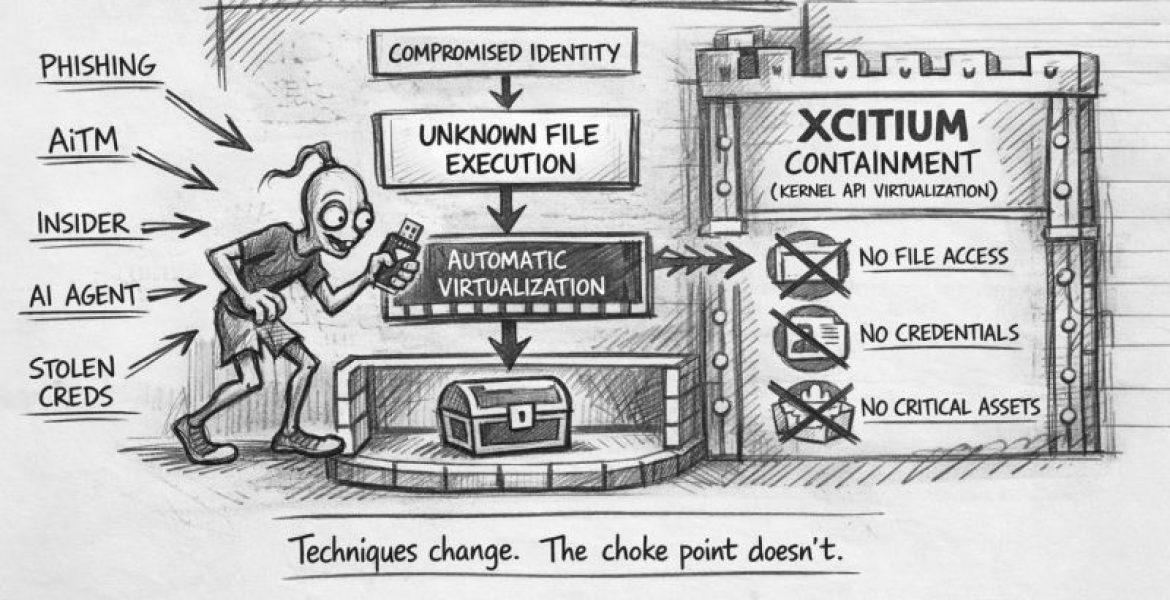
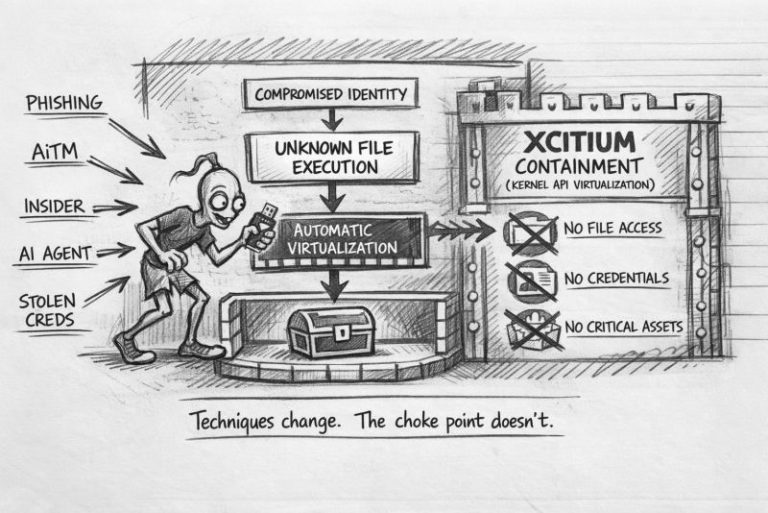











-Phishing.
-AiTM kits.
-Insiders.
-Stolen credentials.
-Compromised AI agents.
So the industry builds more tools to stop those techniques:
-New MFA.
-New phishing detection.
-New identity protections.
-New AI security frameworks.
But every attack eventually needs the same thing:
𝗖𝗼𝗱𝗲 𝗲𝘅𝗲𝗰𝘂𝘁𝗶𝗼𝗻.